
They don’t hack. They log in.
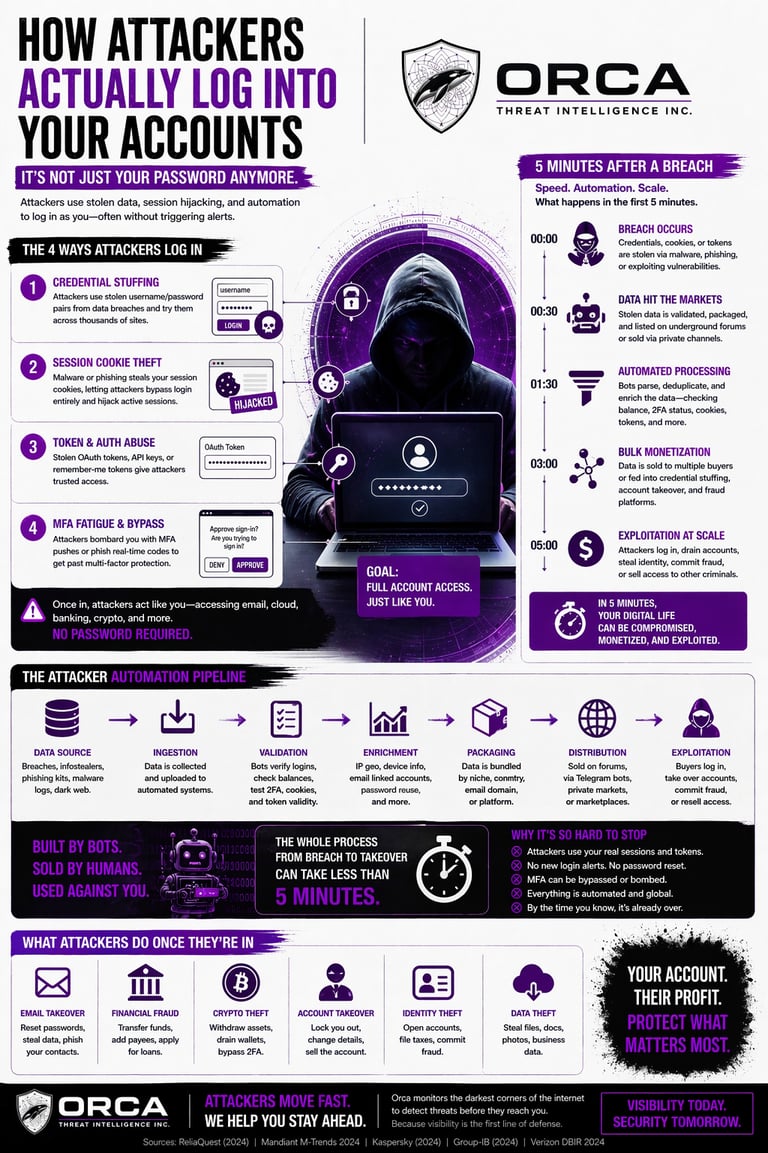
Most people imagine hackers “breaking in.”
That’s not how it works anymore.
Attackers log in using stolen sessions, cookies, and automated pipelines that reuse your data across thousands of services.
No alerts. No guessing. No obvious signs.
Just access — as you.
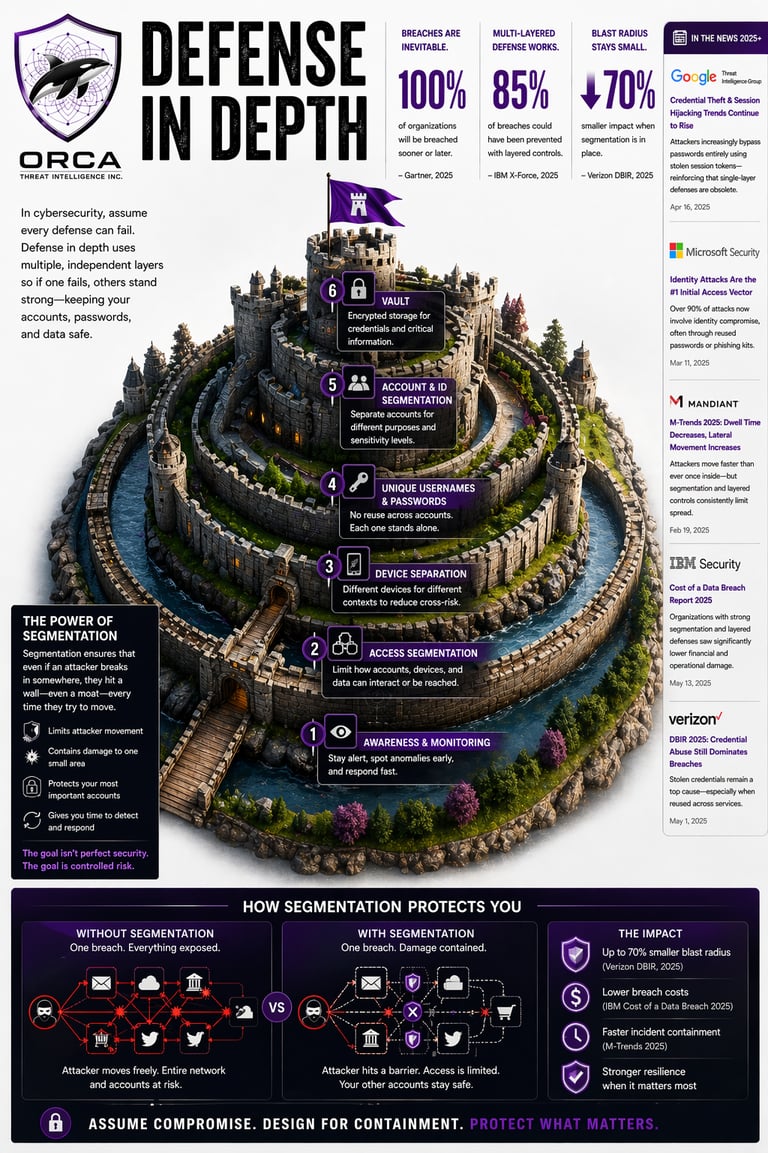
Once attackers can log in as you, a single weak point puts everything at risk.
That’s why security isn’t about one tool — it’s about segmentation.
Each account, device, and identity needs to be isolated so a breach in one place doesn’t cascade into everything else.
This layered approach is what actually stops modern attacks.
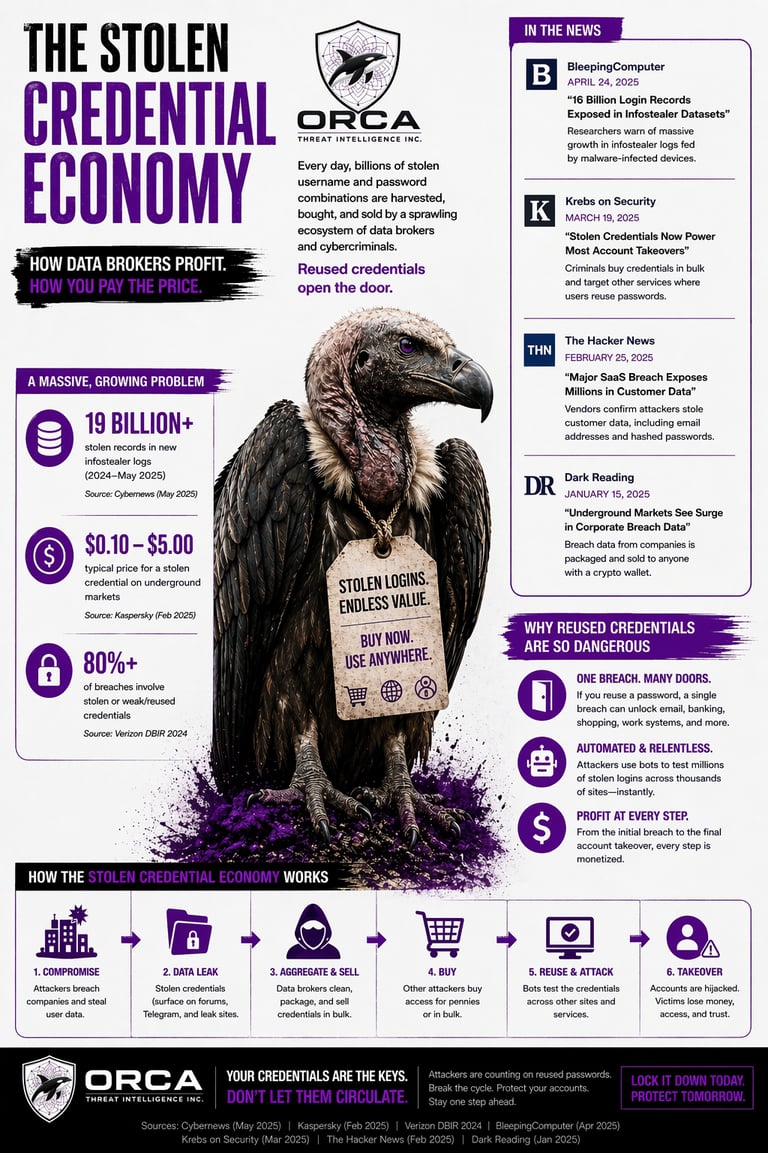
When a company gets breached, your data doesn’t just sit there.
It’s collected, cleaned, and sold through a massive underground ecosystem — where attackers buy access in bulk.
The same credentials get reused across email, banking, shopping, and work accounts.
That’s why one breach can follow you everywhere.

Orca Threat Intelligence
Connect
© 2026. All rights reserved.
